Karim’s problem isn’t solved yet; he still can’t figure out how he will send the letter to Khodeza using a box. Someone suggested that he put it in a box, lock it, and send both the box and the key together. But the problem is, Khodeza’s older brother, Kala Shawkat, could snatch the key away from the courier Ganesh. About a year ago, Karim had given Khodeza a key, but word is Shawkat managed to get his hands on that one too. So what’s the way out?
The Problem of Secret Key Cryptography
lies here … both the sender and receiver must possess the same key. Now, how does the recipient get the key—that becomes the real challenge.
To solve this problem, in 1976, a wandering young man named Whitfield Diffie and a computer scientist named Martin Hellman invented a technique. This method is called Public Key Cryptography. In this system, instead of one key, two keys are used. The mathematical formulas employed here are called one-way functions.
—
It’s something like this—suppose Karim and Khodeza, at separate times (to avoid Shawkat’s attention), both go to Meshkandar Miya, the key seller beside the Dholai canal. Each has a special pair of keys and a special kind of lock made for themselves. The lock is quite unusual: of the two keys Karim has, if the lock is closed by one key, it can only be opened by the second key. The key used to lock it can’t open it again.
Now, Karim and Khodeza’s problem is partially solved. While Shawkat is busy with his university hustles, Karim goes to Ramizuddin’s tea stall in the neighborhood and leaves one of his two keys there. Khodeza, when she gets the chance, also leaves one of her keys at the same tea stall.
Later, when Karim gets the urge to send a grand love letter, he takes his letter and the box straight to Ramizuddin. Khodeza’s key is hanging on a hook in the shop; Karim takes it, packs the letter in the box, and locks the box with that key. He then sends the box with Ganesh.
Kala Shawkat notices Khodeza’s key and even has a copy made on the sly. But even after grabbing the box from Ganesh and desperately trying with that key, he can’t open the box. Annoyed, he assumes this must be a decoy key Karim put there to fool him. When Ganesh finally escapes Shawkat’s clutches and gives the box to Khodeza, she easily opens the lock with her second key and becomes overjoyed reading Karim’s Sharat Chandra-style letter.
—

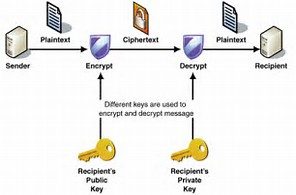
This method of sending letters between Karim and Khodeza is, in essence, public key cryptography. Here, there are two keys—one for locking and one for unlocking. The one used to lock is called the public key. Just as the name suggests, it is public … this key is typically distributed everywhere. On the internet, on many people’s websites or email signatures, you might notice strange strings—something like -GPG-. The more public this key is, the better.
The key used to unlock or decrypt is the private key—highly confidential and never to be shared with anyone. To send a secret message, you have to first find the public key of the recipient. If you find it, you can encrypt the message using that key, and no one but the recipient can unlock its secret. Since a public key can only be used for encryption and not decryption, there’s no harm if enemies get hold of it.
—
So what are the benefits? First—there’s no longer a requirement for both sender and receiver to use the same key, so the hassle of distributing keys is gone. Second—since you don’t need the same key to communicate secretly with someone, you don’t have to carry around a massive bunch of keys for all your friends, and it’s also easier to send messages to strangers. All you need is to find their public key, online or elsewhere. Just encrypt your message with it and send it on.
—
This method was introduced in Diffie and Hellman’s groundbreaking 1976 research paper entitled “New Directions in Cryptography.” It completely revolutionized the world of computer security overnight … the benefits of cryptographic research could now reach people, rather than being monopolized by government intelligence agencies.
It was later revealed that a similar method had been devised years earlier by Britain’s MI5 intelligence agency but was kept secret for national security reasons. Nevertheless, the role of public key cryptography in modern computer security is immense … and it is a core foundation of internet commerce.
—
Well, that’s how messages are exchanged. But how can Khodeza be sure the love letter she received was actually written by Karim, and not a fake letter planted by Ganesh—bribed by Shawkat—posing as Karim’s? How does Khodeza know it’s genuinely Karim’s letter? The answer, next time.






রাকিব ভাইয়া আপনাকে অনেক ধন্যবাদ লেখার জন্য। আমার প্রশ্ন হলো আমি কি প্রত্যেক দিন এটার পরের পর্ব দেখতে পাব?
[email protected]
এর পরবর্তী অংশ কোথায় পাব…..????
বস পরেরটুকু কই
please তারাতারি লিখুন।
I am not clear,
boss parbarti parbo kotai pabo. chabita ki bhabe babohar karbo?